10 Steps to CMMC-AB Certification
Is Your Business Ready for the CMMC?
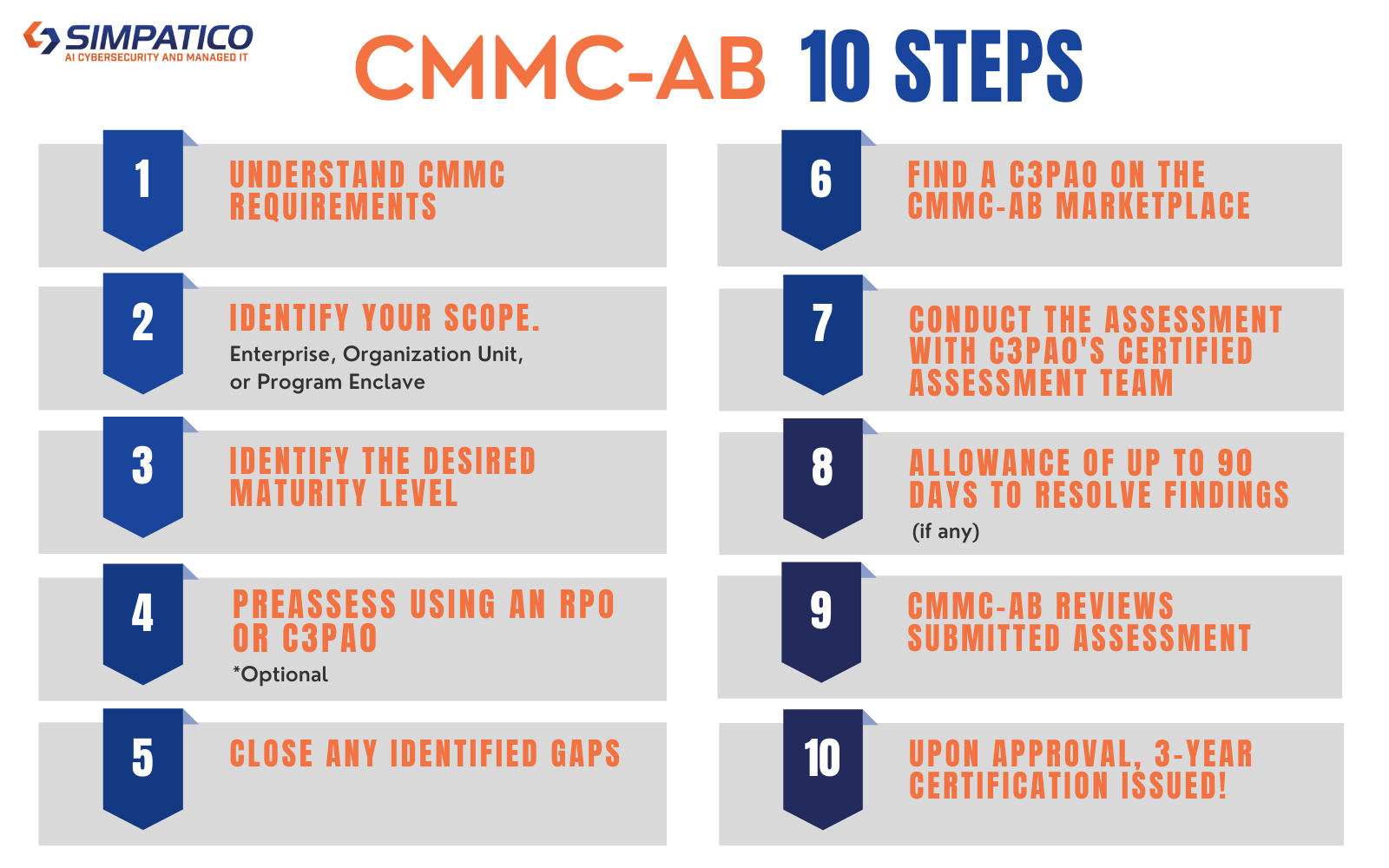
10 Steps to CMMC AB Certification
Step 1.
Understand CMMC Requirements
There are various resources to help you understand the specific CMMC requirements. Sometimes the requirement language and intent is difficult to translate into real world execution and adherence. It is recommended that you reach out to a CMMC-AB Registered Provider Organization (RPO) or Certified Third Party Assessor Organization (C3PAO) which you can find on the CMMC-AB Marketplace, to have them help translate the requirements into terms that you can take action on.
Step 2.
Identify your Scope. Enterprise, Organization Unit or Program Enclave.
A key aspect to ensuring that the confines of the CMMC requirements and assessment are focused on the specific data, network segment, or hosted services, it is critical to ensure that you have accurately identified the scope of your environment as it relates to Federal Contract Information (FCI) or Controlled Unclassified Information (CUI).
- Enterprise – Your organizations entire data/information systems network/ecosystem as is relates to the contract.
- Organization Unit – An isolated subsection or segment of your data/information systems network/ecosystem as it relates to the contract.
- Program Enclave – An enclave approach means the company deploys the technology for protecting CUI to a part of the organization or outside of the organization, like Microsoft GCC High.
When implementing CMMC, a DIB contractor can achieve a specific CMMC level for its entire enterprise network or for particular segment(s) or enclave(s) depending upon where the information to be protected is handled and stored. For companies that need to achieve CMMC compliance, enclave is an ideal way to enable compliance and avoid the challenge and expense of deployment to the whole organization.
Step 3.
Identify your required maturity level.
This will depend entirely upon what level of certification your contract requires and the sensitivity of the information you handle. A point of CMMC is to make it more feasible for small to mid-sized business to become compliant while ensuring that any sensitive information, FCI or CUI your organization handles remains safe.
- Level 1 – Protects Federal Contract Information (FCI)
- Level 2 – Transitions to contain some Controlled Unclassified Information (CUI)
- Level 3-5 – Contains Controlled Unclassified Information (CUI)
Federal Contract Information (FCI)
Federal Acquisition Regulation (FAR) 52.204-21 – Basic Safeguarding of Covered Contractor Information Systems
- FAR 52.204-21 imposes a set of fifteen (15) basic cybersecurity controls for contractor information systems upon which Federal Contract Information (FCI) is stored, processed or transmitted, CMMC L1 added two additional controls.
- Federal Contract Information (FCI) is defined as information provided by or generated for the Government under a contract to develop or deliver a product or service for the US Government.
- These Federal Acquisition Regulation (FAR) cybersecurity controls form the basis for the Cybersecurity Maturity Model Certification (CMMC) Level 1 that is focused on protecting Federal Contract Information (FCI) and Covered Contractor Information Systems (CCIS).
- Federal Contract Information (FCI) can’t be a tangible good or service but it can be the specs or description of that good. The assumption is that all information is not intended for public release unless marked as intended for public release. Treat this information at a minimum, as protected Federal Contract Information (FCI).
- The same rules exist for data developed for the government of in support of a contract. This information should be protected as Federal Contract Information (FCI).
Controlled Unclassified Information (CUI)
Defense Federal Acquisition Regulation Supplement (DFARS) Clause 252.204-7012, Safeguarding Covered Defense Information and Cyber Incident Reporting
Information the Government create or possesses, or that an entity creates or possesses for or on behalf of the Government, that a law, regulation, or Government-wide policy requires or permits an agency to handle using safeguarding or dissemination controls.
Step 4.
Pre-assessment using an Register Provider Organization (RPO) or Certified Third Party Assessor Organization (C3PAO)-(Optional)
Simpatico Systems is an RPO and will work directly with the you to perform a limited CMMC Gap Analysis focused on reviewing the elements of the cybersecurity framework. This review is intended to identify “gaps” or areas of need in complying with the CMMC requirements. Specifically, the assessment will be used to perform the following:
- Assess and determine your overall compliance with the required CMMC level requirements.
- Understand what protections there are for systems, servers, and workstations in the organization and determine their effectiveness.
- Determine what services are in use by your organization such as ISPs, cloud services, and material suppliers which may fall out of scope but could lead to critical network security weaknesses.
- Verify the provided known network configuration and mapping and hardware software asset inventory provided by the Client
Step 5.
Remediate any identified gaps.
After the Gap Analysis has been completed, you will have a clear understanding of the strengths and areas needing improvement as it relates to your specific level of CMMC. The next step is to correct the areas discussed in the Gap Assessment. Remediation efforts can be completed by you in-house or can be completed through an engagement with Simpatico.
Step 6.
Find a C3PAO on the CMMC-AB Marketplace.
Once you have determined any gaps, remediated them, are confident in being able to demonstrate compliance, and can provide two forms of objective evidence for each of the controls required by your level of CMMC, the next step is to engage a Certified Third Party Assessor Organization (C3PAO).
You can find this resource by visiting the cmmcab.org website, navigating to the Marketplace, and selecting C3PAO from the drop down menu. The C3PAO will walk you through the what the engagement with their organization will look like and you can schedule the official CMMC assessment.
Step 7.
Conduct the assessment with C3PAO’s Certified Assessment Team.
The C3PAO will visit your organization and perform the respective CMMC level assessment.
Step 8.
Allowance of up to 90 days to resolve findings (if any).
- Organizations Seeking Certification (OSC) have 90 days to remediate minor issues that prevented certification
- C3PAO must agree that the issues are of a nature that can qualify for remediation
- Assessment Team/Lead Assessor may need to return on site to finalize any remediation
- After any issues are remediated (where appropriate), Lead Assessor finalizes assessment report
- Assessment report is submitted to C3PAO
Step 9.
CMMC-AB reviews C3PAO’s submitted assessment.
- The CMMC-AB receives the assessment report and recommendations from C3PAO.
- If recommendation is to issue a certification, the CMMC-AB performs independent QA review of assessment report and recommendations.
- If the review confirms that the assessment report content is sufficient, then the CMMC-AB will issue a certification to the OSC.
Step 10.
Upon approval, 3-year Certification issued!
If you have made it through steps 1 – 9 successfully, you will be issued and official certification from the CMMC-AB that will be good for 3 years for the applicable CMMC level assessed.
